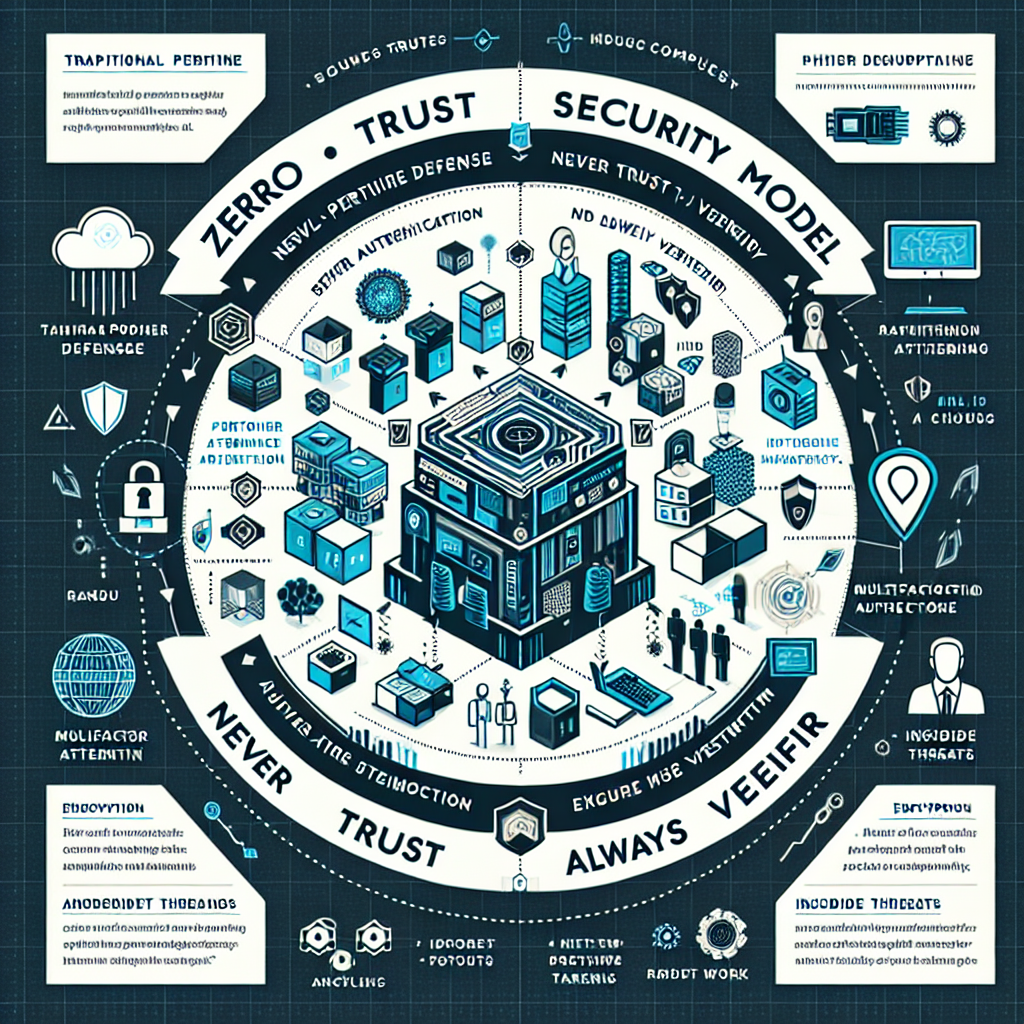
In the rapidly evolving world of cybersecurity, the Zero Trust Security Model is gaining substantial traction as a pivotal approach to securing information systems. This model, based on the principle 'never trust, always verify,' is seen as the antidote to traditional security models that often rely too heavily on perimeter defenses.
In recent days, major data breaches have underscored the need for a more robust security framework. Companies are increasingly adopting Zero Trust architectures to minimize vulnerabilities, particularly in environments where remote work and cloud solutions are predominant.
One prominent case illustrating the efficacy of Zero Trust is Google’s BeyondCorp initiative. After facing persistent security threats, Google transitioned to a Zero Trust model to fortify its internal systems, reaping substantial benefits in terms of enhanced security and operational flexibility. This move has inspired many corporations worldwide to reconsider their security postures.
Furthermore, the increasing sophistication of cyber threats has forced a reevaluation of existing trust assumptions. The rise of ransomware, phishing attacks, and insider threats signifies a need for security models that prioritize authorization and verification at every network stage. The Zero Trust model embodies this ideology by ensuring that each access request, whether originating internally or externally, undergoes rigorous verification protocols.
Businesses contemplating the integration of a Zero Trust model should begin by identifying their most critical data assets and systems. Following this, implementing stringent access controls and leveraging technologies such as multifactor authentication, encryption, and identity management becomes essential.
The integration of AI-driven analytics can further enhance Zero Trust architectures by providing real-time insights and adaptive responses to potential threats. This proactive approach to threat mitigation is crucial in staying ahead of cybercriminals.
As digital transformation initiatives continue to expand, the Zero Trust model is poised to be the cornerstone of modern cybersecurity strategies. It offers an invaluable framework for organizations seeking to mitigate the risks associated with decentralized and cloud-based environments.
Understanding the Latest in Zero Trust Security Models in Today's Cyber Landscape Featured
 Explore the latest insights on the Zero Trust Security Model and its growing importance in cybersecurity, especially in light of recent high-profile data breaches.
Explore the latest insights on the Zero Trust Security Model and its growing importance in cybersecurity, especially in light of recent high-profile data breaches.
Latest from Security Tech Brief
- Emerging Cybersecurity Challenges for Remote Workforce
- The Rise of Zero Trust Architecture in Corporate Networks
- Navigating the Rise of Ransomware Attacks: A Cybersecurity Wake-Up Call
- Collaboration in Cybersecurity: Guarding Digital Frontiers Together
- Strengthening Cybersecurity Frameworks Amid Rising Threats
